Last Updated: 29/10/2019
In the last few months I have been coming across the management and security of Mobile Device more often. This conversation generally leads down two areas that contribute to the overall security of mobile devices. Firstly, the MDM (Mobile Device Management) side and secondly the MTD (Mobile Threat Defense) side. Each of which provides a piece of the puzzle when it comes to managing and securing your users mobile devices. This article will focus on these two technologies and what they can and cannot do.
Mobile Security Threats
Before we start talking about security controls and products that can help secure our devices, lets look at some of the threats first, just so we can understand what we are protecting against.
Mobile device threats have been on the rise for some time, and seeing as everyone has a mobile device which is capable of doing pretty much everything a traditional laptop and PC can do, it makes it a perfect target for cyber criminals.
Lets look at some of the mobile threats we have seen and how these can affect mobile devices.
Data Leakage & Information Skimming
Data leakage is always going to be one of the most common threats within IT, when we implement security, we are generally protecting our data and services. Generally, data leakage on mobile devices is associated with applications that have too many permissions. These are normally free apps that are hosted in the App Store/Play Store that appear as legitimate apps, but in the background they are sending your personal and corporate data to a remote system. This information is then either sold or mined.
Applications with to much permissions could be malicious and steal your data. This is always a concern, especially in BYOD deployments.
Rogue & Unsecured WiFi
We all have the habit to connect to WiFi when we can, as we don’t want to chew through our own data. Now this is fine if you are connected to a trusted WiFi spot, like your home or your office. However, free WiFi networks are generally open and unsecured. Whats worse, is we can have attackers spoof these free WiFi access points and capture data that passes though by performing a Man in the Middle attack (MITM).
SMS and Email Phishing
Similar to desktops and laptops, mobile devices are of course susceptible to phishing attacks. These attacks do not have to be delivered by email, but by SMS too. If a user takes the bait and clicks on a phishing link then this could trick the user to giving up their credentials and some exploits even allow attackers to compromise the whole device. This can then cause data leakage and can also act as a foothold for further attacks and lateral movement.
There are a number of different attack vectors when looking to compromise a mobile device, the above is not an exhaustive list by any means, but should give an indication of some of the attacks that we have seen.
Mobile Device Management (MDM) & Mobile Application Management (MAM)
MDM is a security tool that has been round for a while. MDM provides IT Administrators with the capabilities to monitor, manage and secure user mobile devices. MDM is similar to Group Policy in some ways, except its aimed at mobile devices and tablets. It similar to GPO in the respect that it allows IT administrators to push device configuration policies to make the device DO something. For example you could enforce a PIN code or enforce encryption of the device. This in turn ensures that the enrolled device is secure, as it is following a baseline level of configuration.
There are two distinct areas to keeping mobile device secure within an organisation, these two areas are the configuration and the protection of the device. We all know the first one, configuration, with the likes of MDM (Mobile Device Management) providers such as Intune & Airwatch. MDM providers allows business to control and configure mobile devices, as well as enforcing a level of compliance to the device. For example, you can enforce the use of a PIN Number, dictate which applications should/shouldn’t be installed and ensure that the device is kept up to date with updates, before letting the user access corporate data.
However, MDM is just one part of the security solution, as all it delivers is configuration. Configuration is important to keep security surface area to a minimum, however with more and more threats being aimed at mobile devices we require an additional layer of protection that focuses on the threats themselves. This is where MTD (Mobile Threat Defence) comes into play, MTD provides the additional context and protection against installed applications, device configuration and networking traffic. It is purposely built to look at malicious behaviour and prevent mobile breaches from occurring.
MDM is generally one part of a puzzle, in that Mobile Device Management solutions generally couple in Mobile Application Management functionality to provide a more functional solution that can secure and control both the Device and the Applications. If the security is baked into the application, then the application can technically be used by any device and still be secure. This helps drive BYOD (Bring Your Own Device) deployments for users wanting to use their personal devices.
MDM can also apply to personal devices, however most people do not want IT to push configurations and enforce policies on their personal devices. In this case, MDM can be used to perform a ‘health check’ of a device to ensure that the device is suitable or compliant enough the access corporate resources. This is called a compliance policy, where a device needs to prove that it is compliant before being granted access. For example, IT can allow access to emails on your personal device, so long as that device has a PIN Code, is Encrypted and not Jail-broken or Rooted. This gives IT more control or WHAT is accessing there resources, and ensures a base level of security is conformed to when using a personal mobile device to access corporate resources.
This, coupled in with application level security via MAM (Mobile Application Management) ensures that key security controls are layered into the application level, while MDM ensure that the device is configured to a reasonable baseline.
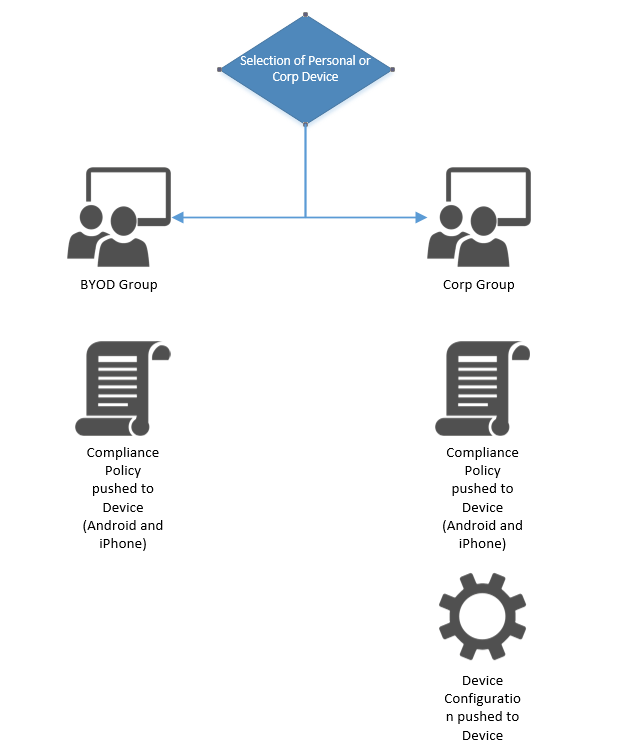
MDM solutions can support a variety of scenarios, including BYOD and Corporate Device Policies. This can generally be done by creating different profiles or groups, based on the device that needs to be enrolled. For example, with Intune you can determine by User Selection or by Device Identifiers if a device is corp owned or personally owned. Depending on what category is selected will determine which compliance policy and device configuration is used. I have attempted to illustrate this below.
Example MDM/MAM Providers
While I do reference Intune in the above section, there are of course alternative MDM solutions. Intune is the one I have used the most, especially since moving to the new Azure portal. Here is a short list of MDM providers:
This is not an exhaustive list, however it highlights a few solutions that I have come across. There are some slight differences between these vendors, so investigation and consideration should be taken when looking at an MDM provider. Key things I look out for when recommending a MDM provider are:
- Enrollment Support – How easy is it to enroll devices? Are there different enrollment methods you can utilise? How easy can we transition and migrate to another MDM provider?
- Interface and Usability – Not much point in purchasing a product that is hard to use, this goes for your end users and your IT admins.
- Licensing and Price – Cost will always be important, investigate the best way to license ie. device vs user. Also see if MDM is part of a bigger bundle that you can utilise.
- Integration with other Products – Especially key for MTD, more on this in the below sections. Solutions like Intune integrate nicely with O365 and can leverage the same identity mechanism.
MDM/MAM Summary
MDM is an important component of IT as more and more users now work from their mobile and in remote locations, making mobile devices another entry point of a breach. Is is important that IT have visibility of what devices have access, as well as being able to control the access to corporate resources. MDM also helps IT with the management and provisioning of mobile resources, acting as the Group Policy of the mobile device world.
While MDM provides a level of security benefits, it focuses more on the configuration of the mobile devices rather than looking at whats on the device and how the device interacts with other applications and data. This is where MTD becomes a requirement.
Mobile Threat Defense (MTD)
Mobile Threat Defense is a growing market within security due to the increased number of threats which compromise mobile devices. While MDM (Mobile Device Management) delivers functionality around the management and configuration of devices, it lacks in the protection of the device from threat vectors. Because of this, it has been increasingly more common to compliment an MDM provider with a MTD (Mobile Threat Defense) provider. By using these 2 solutions, you can leverage functionality in both device management, compliance and protection.
MTD can look at applications and understand if there is any malicious activity, as well as identifying if there is ‘too many’ permissions. Where as the networking parts of MTD can prevent the connection to untrusted or rouge wireless access points. Finally the web content filtering provides a layer of security against browser and web based threats.
When looking at an MTD provider, a key area to consider is the integration with your existing (or future) MDM provider, this provides advantages such as passing back information, but also simplifying management of the tools as they will be administrated from a single console (or pane of glass). Some MDM/MTD providers can do both, which offers some very good benefits for management and administration. But most MDM providers will allow integration into an MTD provider (Which is key to building a strong management and security solution)
For example, Sophos Mobile is capable of doing both MDM and MTD. Where as Microsoft Intune and VMware Airwatch only does MDM. However, Intune can integrate into the likes of Sophos (the MTD Component) as well as other MTD providers like Better, Wandera and Lookout.
The above serves as only a quick example as there are many MDM and MTD vendors out there, the most important part is to consider what can integrate into what. There is no point and no value in using 2 different solutions which have to be managed independently and do not communicate with each other.
Integration with MDM Providers
One of the points I keep mentioning in this article is the integration between MDM and MTD providers being a key consideration. The reason being is that when both of these solutions integrate they can share intelligence between each other, making both solutions more comprehensive.
I have recommended this a number times when planning and implementing Microsoft Intune. As Intune allows the connection to various MTD vendors, it can take the information from MTD and use this within the compliance policy in Intune, allowing Intune to make a decision of granting access based on the reported state from the MTD solution.
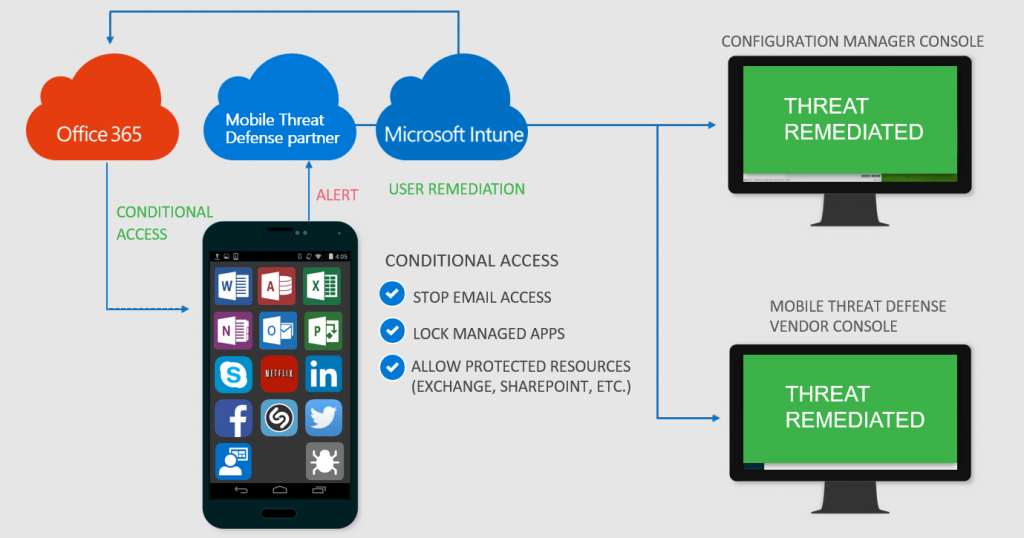
Intune can then leverage the conditional access policies to either prompt for MFA or deny the authentication into corporate resources all together, should a device be reported as non-compliant. All of this fits together very nicely and simplifies the management and security of Mobile Devices.
Mobile Threat Vectors
When we look at mobile security, we can break this down into 4 distinct areas:
- Physical Security – Protection against theft and loss, as well as correct disposal of mobile devices to prevent data leakage.
- Device Security – Protection of attacks that can compromise a mobile device, its OS and its Kernel.
- Network Security – Protection against the networks that Mobile Devices can connect to, as well as malicious web content.
- Data & Application Security – Protection against malicious files and applications that damage or corrupt a mobile device.
While MDM can help mitigate some of the Physical Security vectors (Such as providing remote wipe capabilities), MDM providers will not provide protection against Device or Networking security, although they can help in reducing the attack surface.
Example MTD Providers
Below is a short list of MTD Providers that I have researched and recommended to a number of customer, given that they have good integration with MDM providers like Intune.
General features I tend to look out for when recommending an MTD solution is: How well this can integrate into an MDM provider but also what Mobile Threat Vectors are being scanned (Device, Web, SMS, Network and Data). Some MTD providers have functionality that allows the monitoring of data usage (Wandera), which for some organisations is a useful feature to stop abuse of mobile data limits.
MTD Summary
Given that threats are starting to affect mobile devices and that there is always going to be a natural cross over of users using there personal device for corporate use, it makes sense to consider MTD to compliment the MDM/MAM solutions that are typically used. I have seen some business deploy MTD to personal devices in BYOD projects to ensure that personal devices are compliant when accessing resource and giving IT additional context of the devices that are accessing the network, this of course works out cheaper than buying every user an additional corporate owned device. Whilst some people would argue against deploying applications to personal devices, I have generally seen the user base accept this as it also increases their personal device security (Although this is subject to this being communicated effectively).
MTD is part of the puzzle that fits into MDM to give a more complete security solutions for mobile devices. Given that more and more users are remote and can do a majority of work on their mobile device, it makes sense to bolster the protection of these devices.
Its worth considering MTD if you are planning to do a MDM project, this should be ruled out or in depending on the business risk profile of using mobile devices. When looking at vendors for both MDM and MTD the key things to look for are if the two solutions can integrate and work more effectively.
Thanks for reading!
great post! interesting read on some of the mobile threats and how to prevent them.
Thanks!