Managing Cloud Resources with Sophos Cloud Optix
Now that Sophos Cloud Optix has been officially released, I can now blog about it openly!
Sophos Cloud Optix is a Cloud Management and Compliance tool, mainly geared around infrastructure and platform type services like AWS, Azure and GCP. Sophos Cloud Optix can provide insight to resources and evaluate the compliance of resources based on different frameworks (Including: GDPR & ISO 27001), giving quick access to see how your subscriptions are configured and how these affect the overall security and integrity of the subscription. Further to this, Cloud Optix allows dynamic topology overviews of your Azure, AWS and GCP environments, giving quick visibility to resources in a ‘Visio diagram’ kind of way.
Asides from Cloud Infrastructure services being supported like AWS and Azure, Cloud Optix is also able to support IaC (Infrastructure as Code) environments by integrating with the likes of Github and Jenkins. So if you are deploying and managing resources the traditional way or the new way, Sophos Cloud Optix can support these deployment methods.
In this article I am going to write about my experience with Cloud Optix, from implementation/integration to usage.
Integration to Azure
For my test account, I chose to Integrate into Azure. I will also be integrating into my AWS account, but for this article I chose Azure. The integration was simple to do, while it did include the use of Azure’s Cloud Shell, the process and commands were well documented and functioned correctly.
As you can see from the below, once navigated to settings > Add environment, Optix will provide a clear set of instructions to add your environment in.
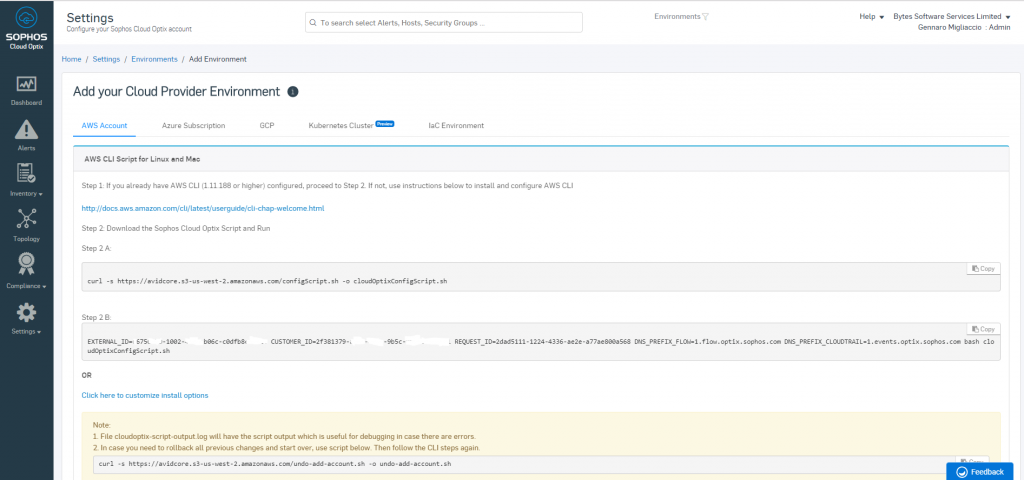
For AWS you will require the AWS CLI and for Azure you will need to use the Azure Cloud Shell.
One point that should be mentioned here is for Azure there is a choice to enable flow logs. While flow logs are very useful for tracking traffic in the topology view (As we will cover later) there is a Azure cost associated with this. Should the additional cost be an issue, you can turn it off from here. Sophos also provide context on this option within the instructions, as you can see from the below screen clip.
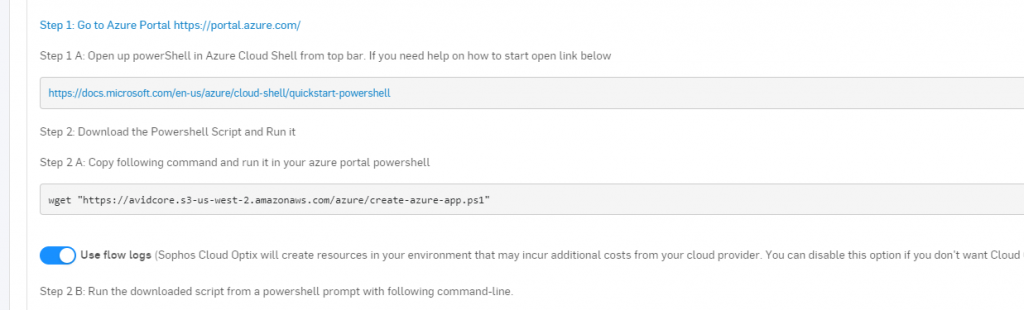
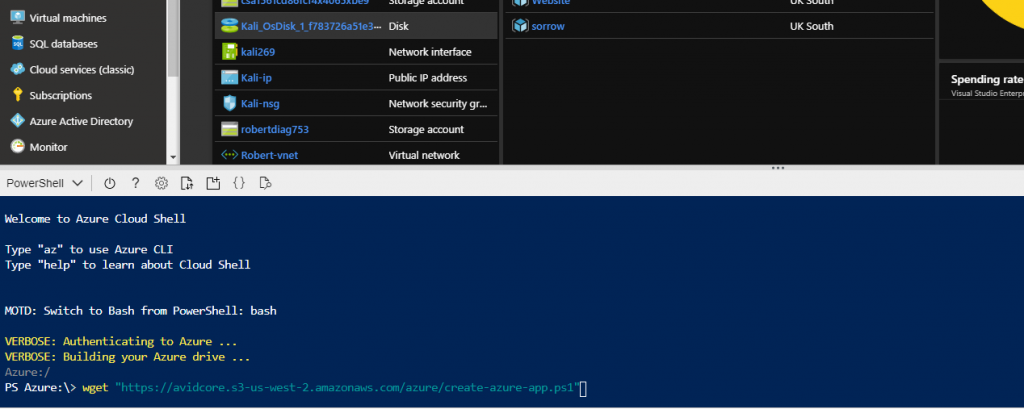
Within Azure and using the Azure Cloud Shell, I simply copy and pasted the commands in (As the commands are customized to your Sophos Cloud Optix Environment).
Note: Make sure you have Global Administrator and Subscription Owner privileges before running the script.
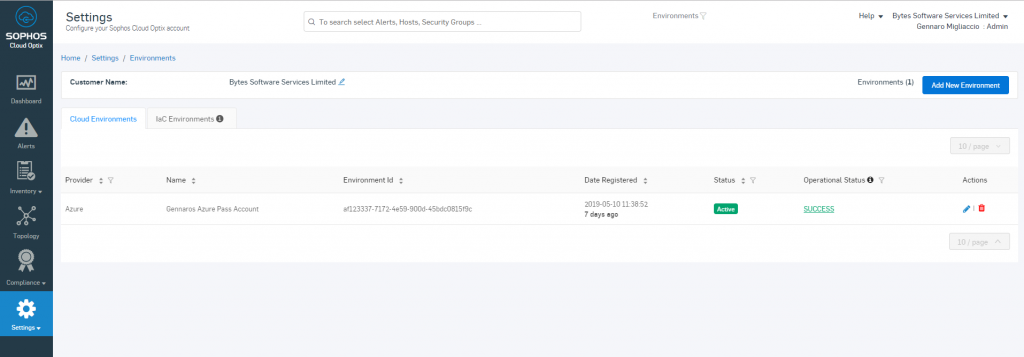
Once the script has run, I noticed the Azure environment in my Cloud Optix showed up almost instantly and took about 10 minutes to start populating the inventory and complete a scan of the environment.
Exploring Sophos Cloud Optix
Now that my Azure Environment is added, its time to start exploring Cloud Optix and some of the insights it pulls back. For the purposed of testing, the Azure environment that is built has a number of ‘Issues’ to test Sophos Cloud Optix. These are issues such as: Resources having Public IPs, Misconfigurations, Poor Architecture and Default Security being lowered. Lets see what Sophos Cloud Optix picks up.
Topology Overview
Firstly, I want to see what information about my environment Sophos Cloud Optix has pulled through and how this looks visually. As you may of experienced within Azure, its very easy to amount a long list of resources with no easy way to see how these connect with each other, unless you drill in to each resource and map this yourself.
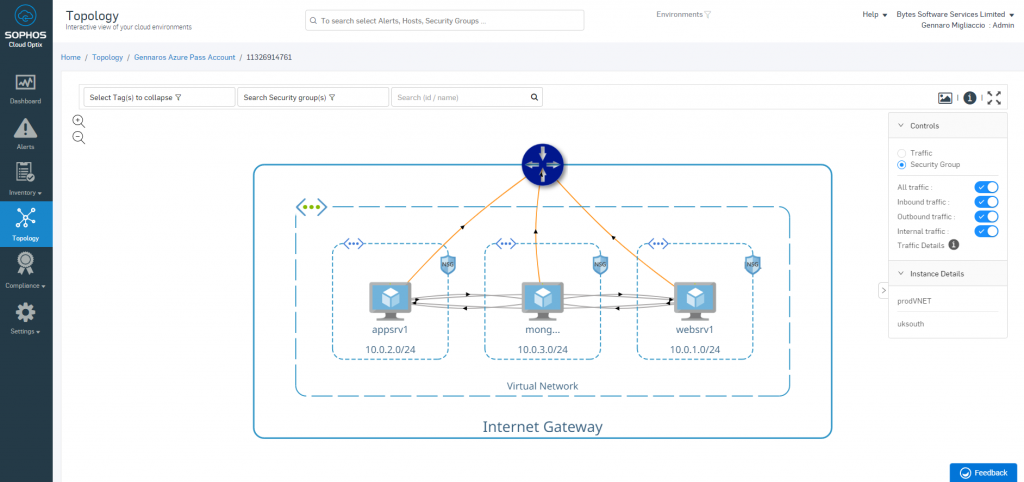
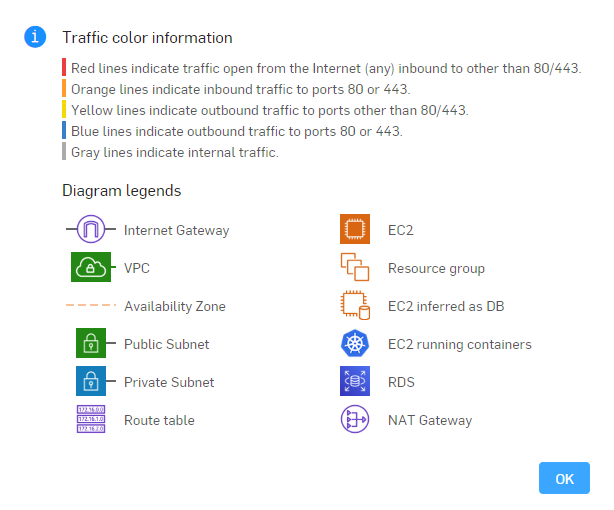
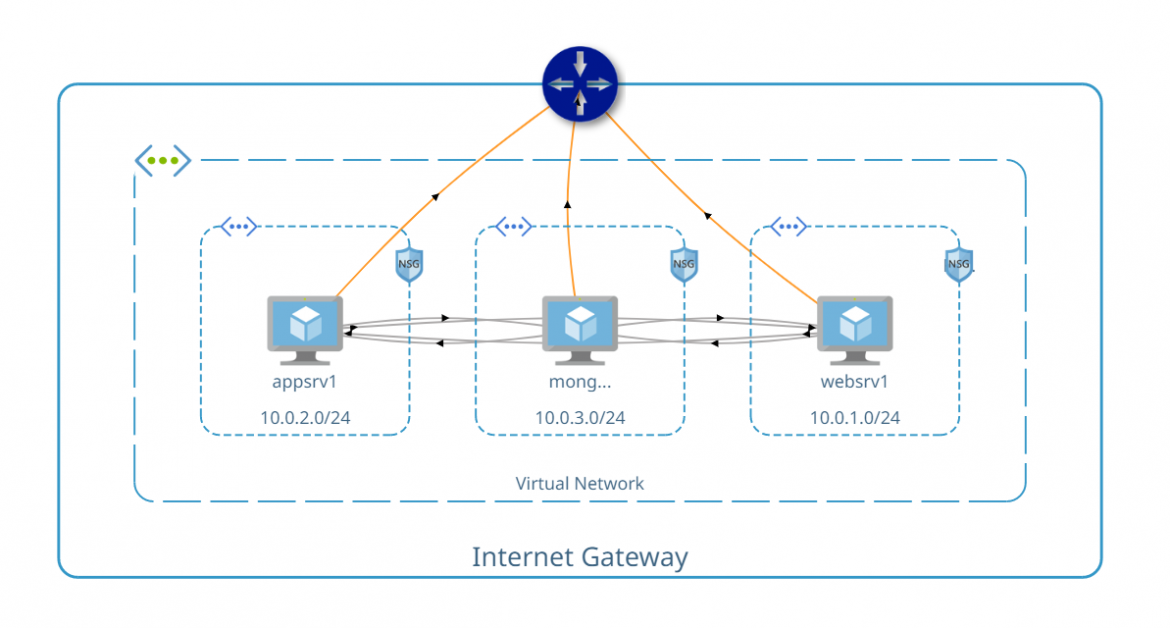
As you can see from the below, it visualizes my Azure resources in a Visio Diagram type of way. As well as showing the flow of traffic from the security group configurations and from the flow logs. Please note that I only created a single Virtual Network, with more Virtual Networks you would be able to see the traffic flow between these.
This is the same with resources deployed in AWS, Sophos Cloud Optix illustrates the resources in an easy to consume way.
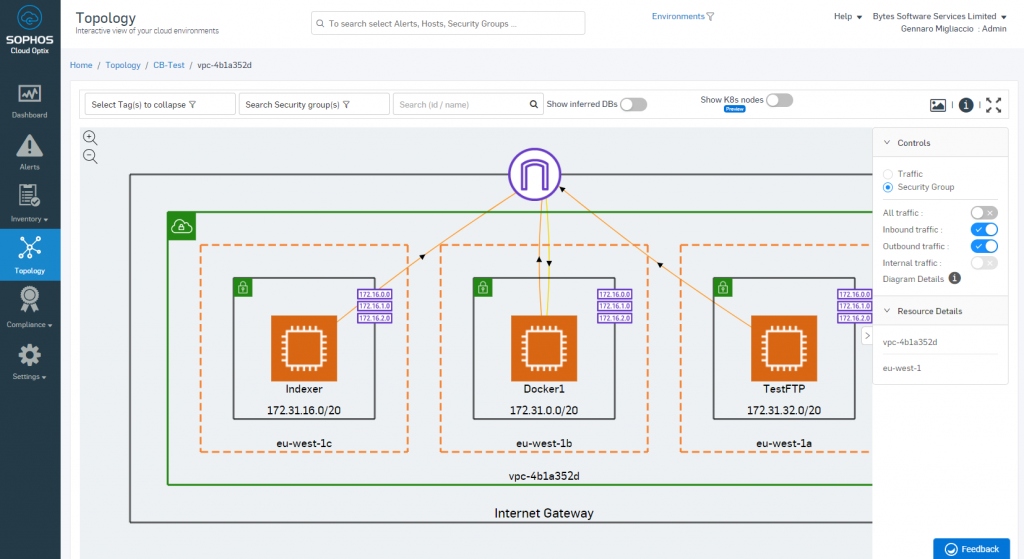
This makes a massive difference in terms of visability and getting a picture of where my resources are, which groups they are part of and most importantly how they connect with each other. I find that when I use the Azure Management Portal and AWS Management Portal my resources are simply listed out, now while I can drill into these resources to get more detail, its still text based detail. This makes it hard to quickly visualize what resources are connected to and communicating to. Unless I start drawing it out on my notebook or designing a diagram in Visio, which would involve an element of human error and constant maintenance to keep up to date.
Below is a snip of the Azure portal with the list of resources, you can quickly see how much easier it is to understand with Cloud Optix.
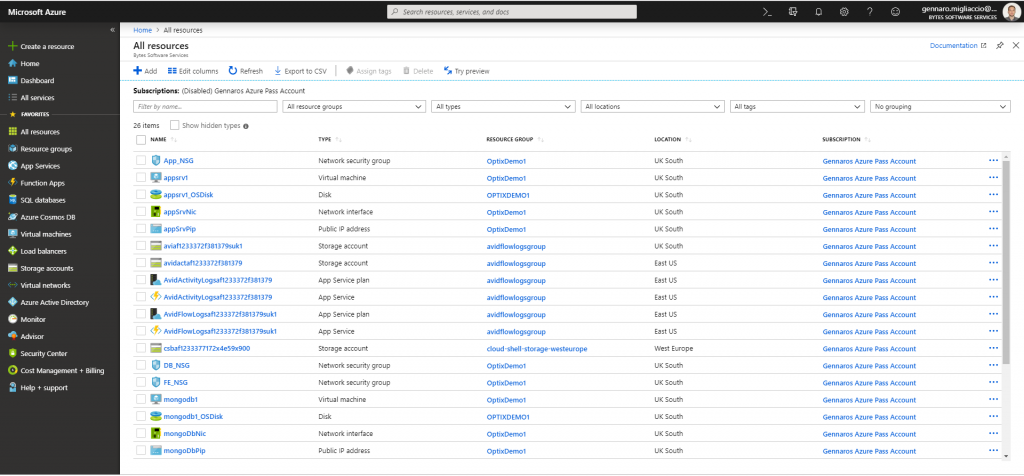
It should be noted, that while Cloud Optix does give an easy to read and understand view of your Azure environment, it will not pull every single detail of every single resource. The Azure Management Portal will still need to be used for advanced information and configuration. Therefore Cloud Optix is not a replacement for the Azure or AWS Portal, but more of a complimentary management layer capable of giving a high level architectural overview of resources and how they connect with one another. In my opinion, it makes life easier, especially with the more resource you have. I only have 3 VMs in this instance and the Azure Portal has a long list of resources, imagine what happens when you have 30 VMs? or even 300?
Compliance and Reporting
Within the compliance tab, you can quickly see how compliant your tenancy is to known industry standards such as GDPR and PCI DSS. From this tab you can see what area failed and which resources are affected. This allows for a very quick method to identify configuration errors and help to align your tenant to best practices, as well as remaining compliant.
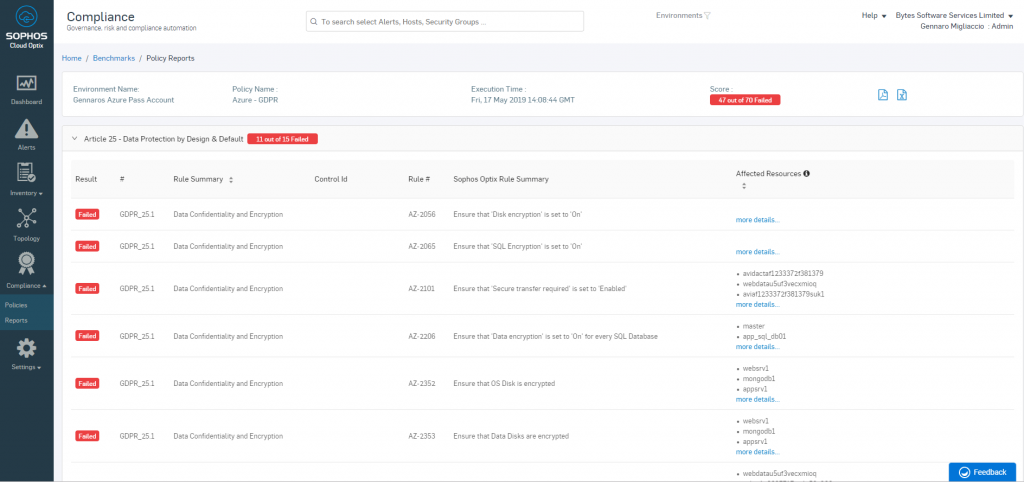
The compliance piece is rule driven, but as you can imagine Sophos has pre-packaged and created a number of rules already, so there is quite a bit that is available out the box. These rules are all enabled by default, but can be switched off or suppressed if needs be. You can also configure your own custom rule set.
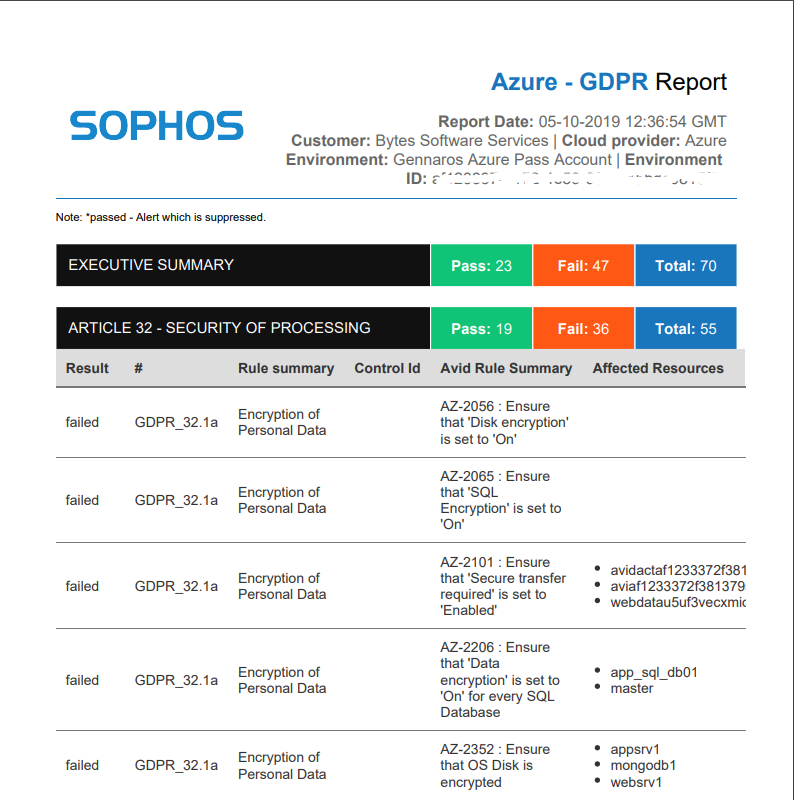
You can also export reports on compliance to give a point in time view of compliance and even send around to the teams! See below for a screen clip of the GDPR output report.
The individual report elements that notify of issues also appear in the alerts section of Sophos Cloud Central, while I will cover in the next section.
Alerting
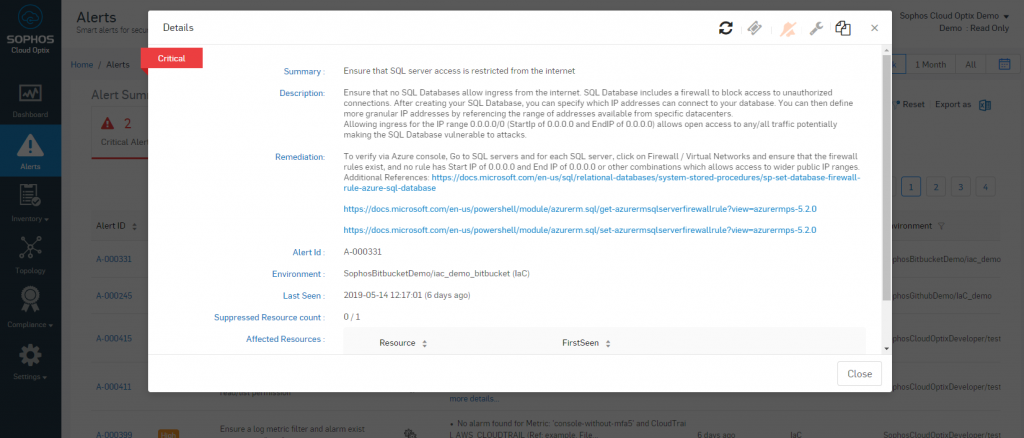
All of the report elements are based on rulesets, however when a tenancy fails an individual rule, this is flagged in alerts. Alerts organise the severity of the failure, as well as providing details on the affected resource and providing some guidance for remediation. It should be noted that Cloud Optix will not go off and do the remediation, although I suspect there will be scope for this in the future or at least an option to kick off a runbook or script within the Azure environment.
From the below, you can see the alerting dashboard within Sophos Cloud Optix.
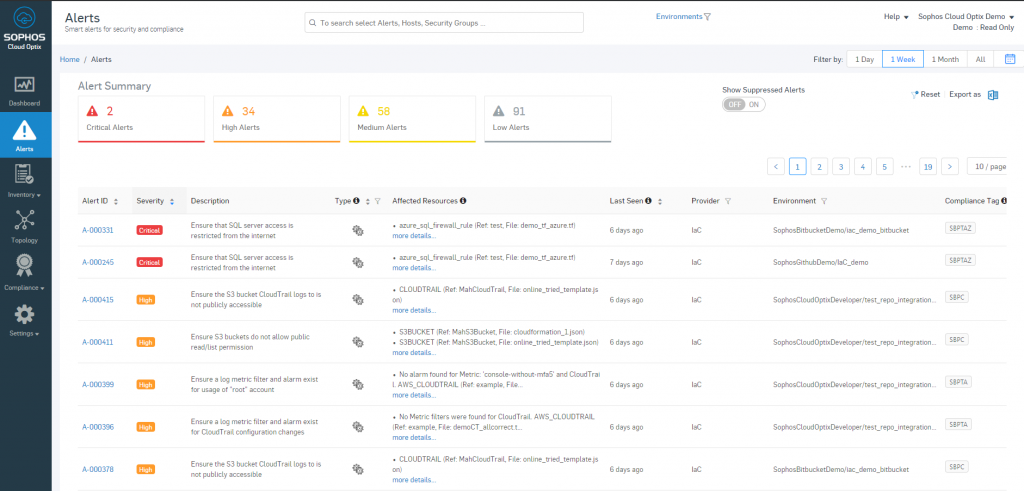
The alerts dashboard gives a nice overview of the different areas that need attention, based on the configured rulesets. Cloud Optix provides guidance for remediation, when each of these alerts are clicked and drilled into.
If integrations are setup, then the alerts can also be piped into a Service Desk tool, such as ServiceNow. Seeing as these alerts are raised based on a ruleset, you can also suppress alerts and white-list individual resources. Therefore an element of tuning and management will be required when using the alerts section.
Azure Native Vs. Sophos Cloud Optix
Its worth noting that Microsoft Azure also has some similar functionality to Sophos Cloud Optix with their Security Center. The capabilities of Azure Security Center allow the assessment of resources to see if these hit a compliance ruleset and can feedback on these.
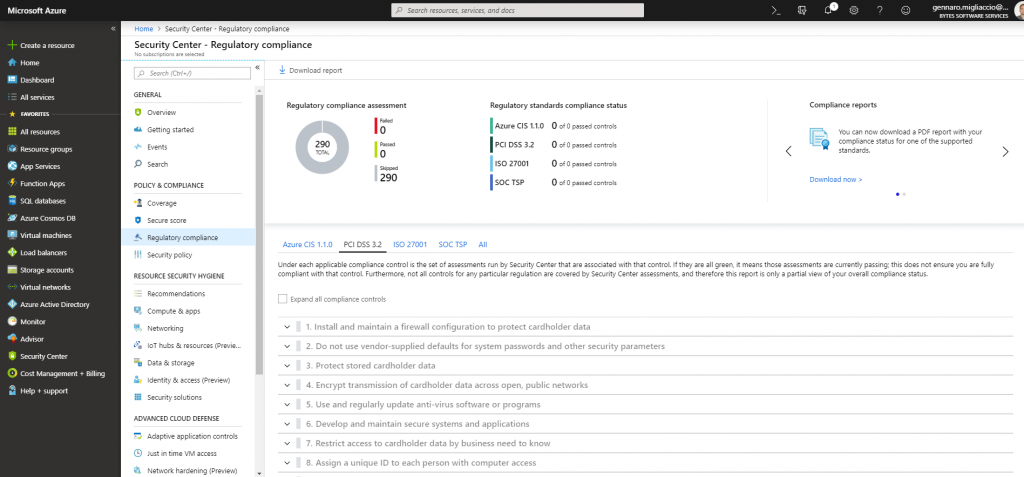
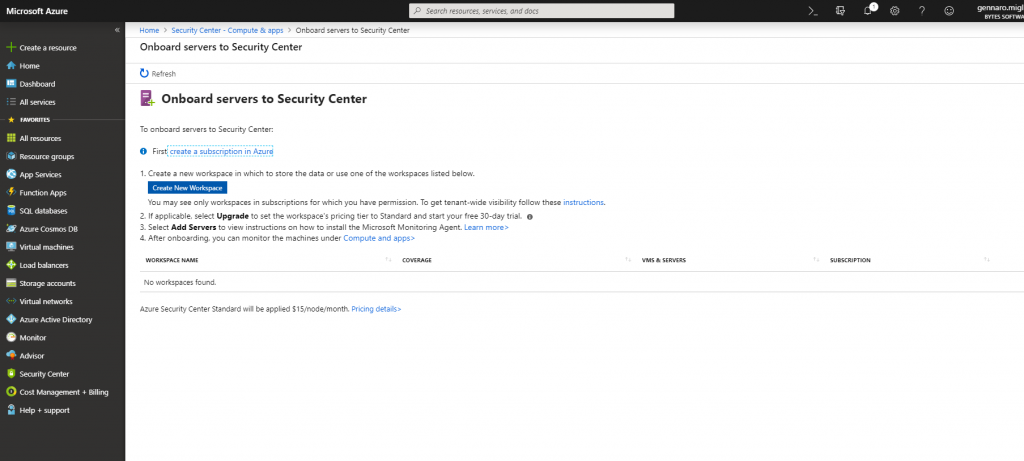
In terms of setup and deployment, Sophos was very straight forward, however I struggled a little with the Azure Security Center as it seems like you have to Onboard Servers into the Security Center by deploying an agent. Now, I can understand an Agent will pull back more information about the server, however Sophos Cloud Optix did not require any agent deployment, only access to the tenant subscription.
Azure Security Center is a chargeable service, much like Sophos Cloud Optix, however I do not have enough information on different price points for a full comparison.
All in all, Azure does seem a little more confusing to setup and requires additional steps to deploy an agent down to the individual virtual machines. I also couldn’t see any support for Infrastructure as Code repos like github, as well as the obvious of being for Azure only, no AWS or GCP (Although, you may be able to do this from an agent level, not a tenant level). Sophos Cloud Optix has the advantage of functioning on the tenant level with support on multiple different cloud vendors and code repos, giving a holistic view into your cloud compliance.
Summary
Hopefully this article will give insight to what Sophos Cloud Optix can offer. In my opinion, Cloud Optix is a helpful tool that can overlay the likes of Azure, AWS and GCP to provide quick and actionable insights within a Cloud environment, based on known compliance frameworks. Its main intention is to drive compliance and increase visibility within an organisation, by providing an overview into correct & incorrect configurations as well as mapping out the topology of a cloud environment from the tenant/subscription level (as opposed to the Networking level).
This tool is a great strategic move by Sophos, given that there is a lot of potential to combine this in with their XG Firewall offering. Resulting in network level visibility and allowing pro-active actions to occur, such as isolating resources that are non-compliant. Seeing as this tool is fresh off the press, its interesting to see how Sophos takes this forward and combines it in with their security portfolio.
Please note that this guide was based on the integration to Azure, Sophos Cloud Optix can also support AWS and GCP. Making it a diverse platform for the management and compliance of your cloud resources. I will be updating this article with an integration of AWS and GCP in the future.
Sophos Cloud Optix is available as a free trial and would recommend anyone to get some hands on experience with this tool to get insight on their cloud infrastructure. Click here for the Sophos Cloud Optix home page where a trial can be spun up!
If you require a dummy lab environment in Azure then its worth spinning up a free trial of Azure and deploying the following Github template here. Credit to David Okeyode for putting this lab together for the purpose of testing Optix. The environment will have ‘flaws’ with it to make Optix light up and throw up some alerts.
Thanks for reading and happy testing!
Amazing post Genarro!